http://www.riazhaq.com/2018/05/proliferation-of-cyber-hacking-tools-in.html
Many intelligence agencies are turning to the use of smartphone malware and spyware for the purpose of hacking and surveillance. The list of such agencies includes but not limited to US CIA, NSA, Mossad, RAW, MI6, ISI and others. Global proliferation of cyber hacking tools appears to have been accelerated with the US CIA's loss of control of its hacking tools including spyware, malware, viruses and trojans.
Stealth Mango and Tangelo:
Lookout, an American mobile security firm based in San Francisco, has recently published a report claiming that a "group or individuals that are believed to belong to the Pakistani military "has developed and released a "set of custom Android and iOS surveillanceware tools we’re respectively calling Stealth Mango and Tangelo". The report says: "These tools have been part of a highly targeted intelligence gathering campaign we believe is operated by members of the Pakistani military". The countries affected by it include Afghanistan, India, Iraq, Pakistan and the United Arab Emirates, according to Lookout report.
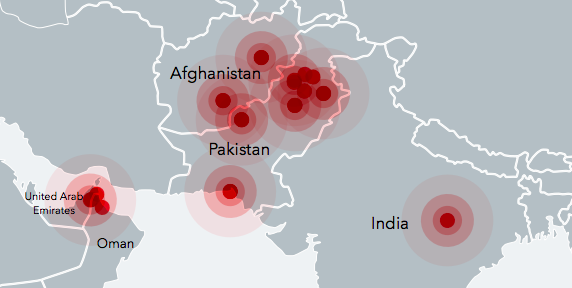
Mango and Tangelo Spyware Targets. Source: Lookout
The targets in Pakistan include members of the foreign diplomatic corps who have visited conflict zones, particularly parts of Balochistan, and Pakistani officials involved in internal corruption investigations.
The goal of the Lookout report is to sell their security software as obvious from their concluding summary below:
"Stealth Mango and Tangelo is yet another example among the numerous campaigns we have uncovered (Dark Caracal, ViperRAT, FrozenCell, etc.) where threat actors are developing in-house custom surveillanceware. The actor behind Stealth Mango has stolen a significant amount of sensitive data from compromised devices without the need to resort to exploits of any kind. The actors that are developing this surveillanceware are also setting up their own command and control infrastructure and in some cases encountering some operational security missteps, enabling researchers to discover who the targets are and details about the actors operating it that otherwise are not as easily obtained. Relevant data has already been shared with the appropriate authorities. Lookout customers are protected against Stealth Mango and Tangelo and have been for several months since the beginning of the investigation."
Amnesty International Allegations:
Amnesty International has alleged that attackers are using fake online identities and social media profiles to "ensnare Pakistani human rights defenders online and mark them out for surveillance and cybercrime". The report titled "Human Rights Under Surveillance: Digital Threats against Human Rights Defenders in Pakistan" claims that Diep Saeeda, a Lahore-based human rights activist, has been targeted by a "network of individuals and companies based in Pakistan that are behind the creation of some of the tools seen in surveillance operations used to target individuals in Pakistan".
Amnesty says that "over the course of several months, Amnesty International used digital forensic techniques and malware analysis to identify the infrastructure and web pages connected to online attacks on human rights activists in Pakistan". "Amnesty International’s Technology and Human Rights team has been able to trace these attacks to a group of individuals based in Pakistan".
Proliferation of Hacking Tools:
In 2017, Wikileaks revealed that the American intelligence agency CIA has "lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized "zero day" exploits, malware remote control systems and associated documentation." The Wikileaks noted that that "the CIA made these systems unclassified".
Wikileaks said: "In what is surely one of the most astounding intelligence own goals in living memory, the CIA structured its classification regime such that for the most market valuable part of "Vault 7" — the CIA's weaponized malware (implants + zero days), Listening Posts (LP), and Command and Control (C2) systems — the agency has little legal recourse".
FBI agents have since arrested 29-year-old former CIA software engineer Joshua A. Schulte as a prime suspect in the release of the CIA documents via Wikileaks, according to New York Times.
It appears that the CIA's "hacking arsenal" is now being modified and used by many state and non-state actors to carry out hacking and surveillance of their targets around the world. The proliferation of cyber hacking tools appears to be a lot easier than the proliferation of the nuclear weapons technology.
Summary:
A report by American mobile security software vendor Lookout claims that individuals and groups connected to the Pakistani military are using spyware and malware tools on targets in Afghanistan, Pakistan, India and UAE. Amnesty International alleges that Pakistan intelligence agencies are "network of individuals and companies based in Pakistan that are behind the creation of some of the tools seen in surveillance operations used to target individuals in Pakistan".
Many intelligence agencies are turning to the use of smartphone malware and spyware for the purpose of hacking and surveillance. The list of such agencies includes but not limited to US CIA, NSA, Mossad, RAW, MI6, ISI and others. Global proliferation of cyber hacking tools appears to have been accelerated when the US CIA lost control of its hacking tools including malware, viruses and trojans.
http://www.riazhaq.com/2018/05/proliferation-of-cyber-hacking-tools-in.html
Many intelligence agencies are turning to the use of smartphone malware and spyware for the purpose of hacking and surveillance. The list of such agencies includes but not limited to US CIA, NSA, Mossad, RAW, MI6, ISI and others. Global proliferation of cyber hacking tools appears to have been accelerated with the US CIA's loss of control of its hacking tools including spyware, malware, viruses and trojans.
Stealth Mango and Tangelo:
Lookout, an American mobile security firm based in San Francisco, has recently published a report claiming that a "group or individuals that are believed to belong to the Pakistani military "has developed and released a "set of custom Android and iOS surveillanceware tools we’re respectively calling Stealth Mango and Tangelo". The report says: "These tools have been part of a highly targeted intelligence gathering campaign we believe is operated by members of the Pakistani military". The countries affected by it include Afghanistan, India, Iraq, Pakistan and the United Arab Emirates, according to Lookout report.
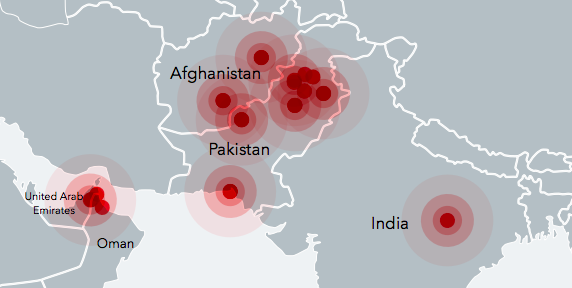
Mango and Tangelo Spyware Targets. Source: Lookout
The targets in Pakistan include members of the foreign diplomatic corps who have visited conflict zones, particularly parts of Balochistan, and Pakistani officials involved in internal corruption investigations.
The goal of the Lookout report is to sell their security software as obvious from their concluding summary below:
"Stealth Mango and Tangelo is yet another example among the numerous campaigns we have uncovered (Dark Caracal, ViperRAT, FrozenCell, etc.) where threat actors are developing in-house custom surveillanceware. The actor behind Stealth Mango has stolen a significant amount of sensitive data from compromised devices without the need to resort to exploits of any kind. The actors that are developing this surveillanceware are also setting up their own command and control infrastructure and in some cases encountering some operational security missteps, enabling researchers to discover who the targets are and details about the actors operating it that otherwise are not as easily obtained. Relevant data has already been shared with the appropriate authorities. Lookout customers are protected against Stealth Mango and Tangelo and have been for several months since the beginning of the investigation."
Amnesty International Allegations:
Amnesty International has alleged that attackers are using fake online identities and social media profiles to "ensnare Pakistani human rights defenders online and mark them out for surveillance and cybercrime". The report titled "Human Rights Under Surveillance: Digital Threats against Human Rights Defenders in Pakistan" claims that Diep Saeeda, a Lahore-based human rights activist, has been targeted by a "network of individuals and companies based in Pakistan that are behind the creation of some of the tools seen in surveillance operations used to target individuals in Pakistan".
Amnesty says that "over the course of several months, Amnesty International used digital forensic techniques and malware analysis to identify the infrastructure and web pages connected to online attacks on human rights activists in Pakistan". "Amnesty International’s Technology and Human Rights team has been able to trace these attacks to a group of individuals based in Pakistan".
Proliferation of Hacking Tools:
In 2017, Wikileaks revealed that the American intelligence agency CIA has "lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized "zero day" exploits, malware remote control systems and associated documentation." The Wikileaks noted that that "the CIA made these systems unclassified".
Wikileaks said: "In what is surely one of the most astounding intelligence own goals in living memory, the CIA structured its classification regime such that for the most market valuable part of "Vault 7" — the CIA's weaponized malware (implants + zero days), Listening Posts (LP), and Command and Control (C2) systems — the agency has little legal recourse".
FBI agents have since arrested 29-year-old former CIA software engineer Joshua A. Schulte as a prime suspect in the release of the CIA documents via Wikileaks, according to New York Times.
It appears that the CIA's "hacking arsenal" is now being modified and used by many state and non-state actors to carry out hacking and surveillance of their targets around the world. The proliferation of cyber hacking tools appears to be a lot easier than the proliferation of the nuclear weapons technology.
Summary:
A report by American mobile security software vendor Lookout claims that individuals and groups connected to the Pakistani military are using spyware and malware tools on targets in Afghanistan, Pakistan, India and UAE. Amnesty International alleges that Pakistan intelligence agencies are "network of individuals and companies based in Pakistan that are behind the creation of some of the tools seen in surveillance operations used to target individuals in Pakistan".
Many intelligence agencies are turning to the use of smartphone malware and spyware for the purpose of hacking and surveillance. The list of such agencies includes but not limited to US CIA, NSA, Mossad, RAW, MI6, ISI and others. Global proliferation of cyber hacking tools appears to have been accelerated when the US CIA lost control of its hacking tools including malware, viruses and trojans.
http://www.riazhaq.com/2018/05/proliferation-of-cyber-hacking-tools-in.html